Commercial Access Control Systems for Small Businesses UK
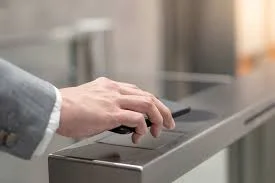
Security is a top priority for every small business. Whether you operate a retail shop, office, warehouse, or healthcare clinic, protecting your staff, assets, and sensitive data is essential. That is why many organisations are now investing in Commercial Access Control Systems for Small Businesses UK to strengthen their security infrastructure. Traditional locks and keys…